A Proven Methodology for Enterprise Risk Allocation
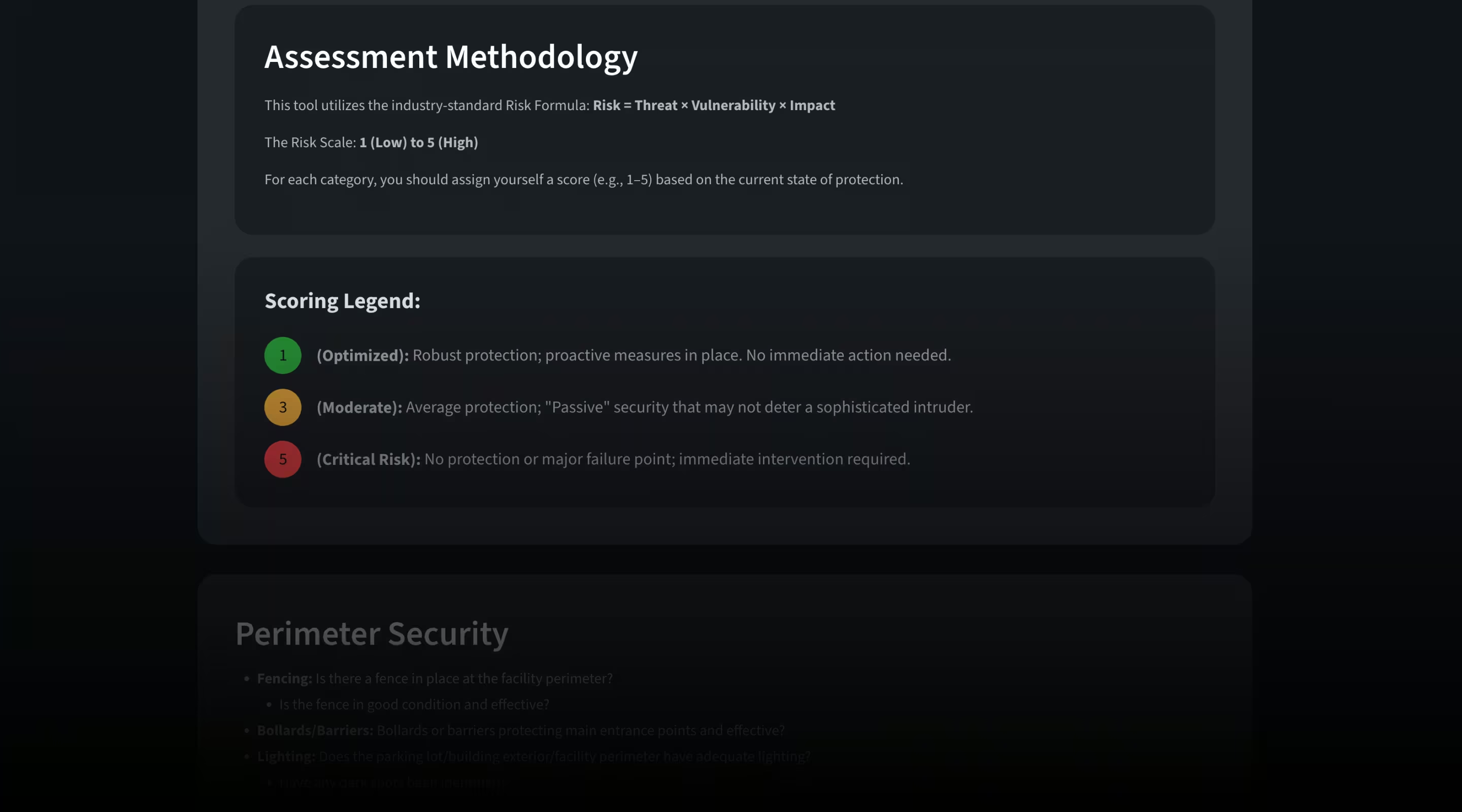
Build a proven methodology for assessing site risk and allocating security resources effectively across your entire enterprise. By using the LVT Risk Assessment Tool, leaders can utilize the industry-standard formula—risk = threat × vulnerability × impact—to audit properties across five critical categories: perimeter security, access control, surveillance and detection, physical assets, and security culture. By inputting your self-assigned risk scores, you can identify potential blind spots and prioritize security investments where they are needed most.

Featured Contributors

Chad Stevens
Chad joined LiveView Technologies (LVT) in 2025, he has held a variety of security roles at ExxonMobil, including leadership roles designing risk management process, technical security design, and development of security policies and procedures. He holds a bachelor's degree from Penn State, University, an MBA from Tulane University, and a master's degree from MIT.

Brady Edwards
Brady Edwards is a security leader with 20+ years of experience in law enforcement and physical security. As AVP of Business and Market Development at LVT, he helps drive security innovation. Previously, he led physical security operations at Northrop Grumman, managing enterprise-wide security programs. A former U.S. Coast Guardsman, he holds a master’s in business administration and is a board-certified Physical Security Professional (PSP).
RSVP Now to Join Us at Snowbird in 2027
Our team is already planning next year's S3 event. Be among the first to secure your spot. Submit your information and stay tuned for updates on an even bigger and better S3 in 2027.
Join us at Snowbird Ski Resort, March 8–12, 2027 for high-altitude gathering of the nation’s top safety and security leaders. Hosted by LiveView Technologies (LVT), this exclusive summit offers a one-of-a-kind opportunity to engage in dynamic group discussions and gain insights from visionary experts in the breathtaking Wasatch mountains. Space is limited to ensure meaningful conversation and impact, so reserve your spot today to help shape the future of life safety while enjoying world-class hospitality and unforgettable views.
RSVP today!
Get the Latest Articles
Unlock exclusive insights from the world of intelligent site management and proactive security. Subscribe to ELEVATE to get our latest featured articles, expert interviews, and tactical insights delivered right to your inbox.
Test Out the Best Security Strategy
We offer a free consultation and a custom end-to-end security strategy for your unique situation. Connect with an LVT specialist to see if you qualify for a risk-free trial.